Sorry, guys.
Useful Idiots
def. see Canadians….
Lead Balloons.
Little Potato’s appeal to the pope to renounce our sins is going over well in Saskatchewan.
Moe said the carbon tax will cost each family in the province about $1,250 a year and the province $2.5 billion, while at the same time threatening jobs in the energy sector.
And it’s carbon dioxide, not carbon. There is a difference, eh.
Sin Tax
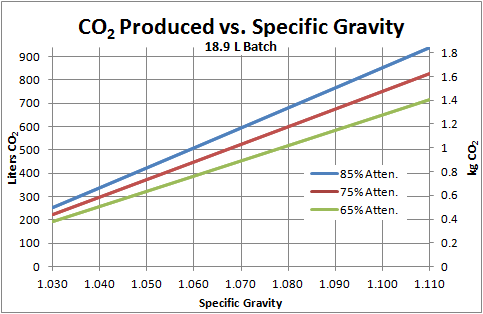
An extra $10/sixty-thousand bottles to start with, and that’s just the brewing process.
Buying indulgencies. #NotACult NoooNoNoNo.
Think the Law is unfair?
Then start action on it against a Liberal MP.
That will get it changed PDQ.
Heh.
The Libranos.
Robyn Urback: A Liberal expense scandal is just like warm milk: familiar, nostalgic and a little bit disgusting. Less than one year into their mandate under Prime Minister Justin Trudeau, the Liberals have offered Canadians more than a few melancholy reminders of what it was, exactly, that earned Stephen Harper the near-decade in power the Liberals are now keen to cast off as an aberration.
Related:
But many voters would conclude that moving expenses should include the costs of having a team of strong people show up at the house, carry its contents into a moving van, haul it all to the new digs, and unload it there. Many of us wouldn’t expect moving expenses to include real estate fees, deed transfer fees and “personal cash payouts”.
Or not….
Reader Tips
Summer is over.
Snow in the forecast for Wednesday….
The Creation of Adam
Settled Science.
Via Naill.
Reader Tips
It’s what liberals do.
After they’ve proved ineffective in office, they can’t ever shut up after they’re a footnote in history.
Ugh
Do you know why they just do reboots and remakes now-a-days?
Because doing anything creative will offend someone.
Via Drudge.
College Football day.
UofS Huskies vs. the UofR Rams at the new Mosaic Stadium.
Saskatchewan’s university team vs the trumped up PFC team.
Go Huskies.
Here we go again.
In today’s political climate there will be no such thing as ‘too big to fail’.
Via Instapundit
Reader Tips
Maybe, just maybe
Stop talking about bimbos and get back to talking about jobs and the economy, stupid.
“Conspiracy Theory”
The Commission on Presidential Debates reported on Friday that there were in fact issues with Donald Trump’s microphone at the Debate Monday evening at Hofstra university in New York.
That Iran deal.
If Obama isn’t bothered to follow it, why should the Iranians?
Like to like
A bit more than, “…their photo taken with thousands of Canadians…”, no?
A few months before being elected prime minister, Justin Trudeau was the featured speaker at a Richmond business lunch sponsored by a company of a Vancouver immigration consultant accused of defrauding Chinese immigrant investors.

